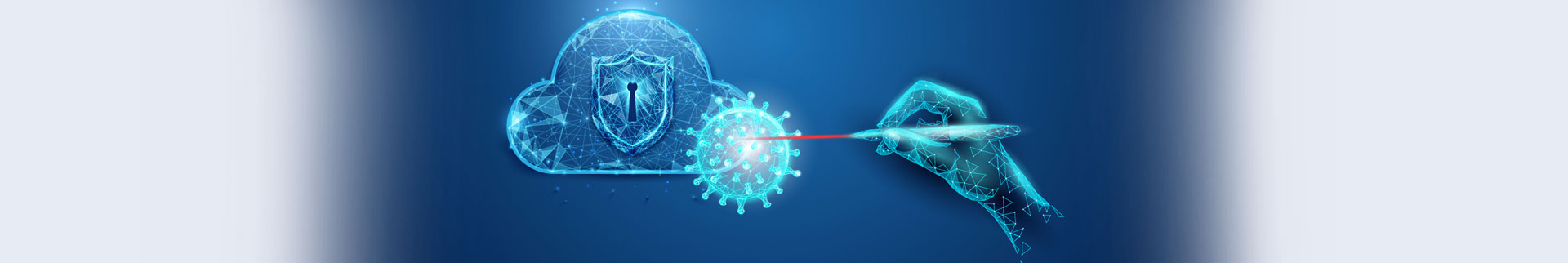
Covid-19 has triggered new layers of intricacies in an already complex IT security landscape. A sudden spike in work-from-home instances means that the threat actors have gained access to a new range of potential vulnerabilities to exploit and attack corporate networks. The developments also have lessons for accelerating AI usage.
This new wave of security challenges is giving endless nightmares to CISOs. With the limited resources and budgets at hand, the fight against the armies of threat actors and threat vectors is now tougher than ever before.
Artificial intelligence (AI)-based tools could help fill up these resource gaps, and thus significantly help CISOs meet their IT security goals.
Here are a few Covid-19-themed IT processes to consider:
Sanitization
In the realm of information security, sanitization is about having a set of access hygiene in place. Typically, many users are not mindful enough of security guidelines when accessing enterprise applications, which increases the chances of the network getting infected.
AI tools could be used to ensure that all user devices comply with the information security hygiene as outlined in the IT or security policy of a given organization. For example, when a user starts a mission-critical application, an AI bot could get triggered, to ensure that the device is not running any other application that has the potential to open a threat window.
Masking
It is important for the CISO to ensure that all data exchanges between the users and the core enterprise IT system are duly masked, say, through a randomly generated end-to-end encryption. This way, it becomes difficult to snoop or hack into a specific device or user.
Quarantine
If, during the course of a session, a given user device gets breached or turns rogue, then an AI tool should be able to trigger a circuit-breaker so that the device under consideration is quarantined from the rest of the user community. This ensures that even if a malware affects a part of the ICT infrastructure, the artificial intelligence tool stops it from spreading to the rest of the system. The CISOs could then focus more on cleaning and restoring the affected part of the system, rather than firefighting to contain a potentially dangerous spread. It goes without saying that this also saves the organization from a likely downtime.
Lockdown
If, despite all preventive measures, a hacker or a malware manages to bluff the AI (as well as the CISO’s team) and succeeds in attacking the IT system, then the AI agent should at least be able to trigger an automated lockdown of all information systems. At the same time, alerts should go out to the designated members of the incident response (IR) team. The IR team could then spring into action, starting with a study of the log maintained by the AI agent. The AI tool comes handy here too. It helps accelerate the action plan of the IR team for reducing the downtime and ensuring business continuity during the downtime.
While CISOs have long been evaluating different applications of AI, it’s time that they should consider it more strategically. Covid-19 lessons for accelerating AI usage in information security can be particularly useful in sectors such as banking, R&D, defense, and among others.







0 Comments